Adaptive Security Model for Data Protection Using Behavioral User Authentication
DOI:
https://doi.org/10.29304/jqcsm.2026.18.12651Keywords:
Authentication, LSTM, Autoencoder, keystroke, Micro-Behavior Intrusion DetectionAbstract
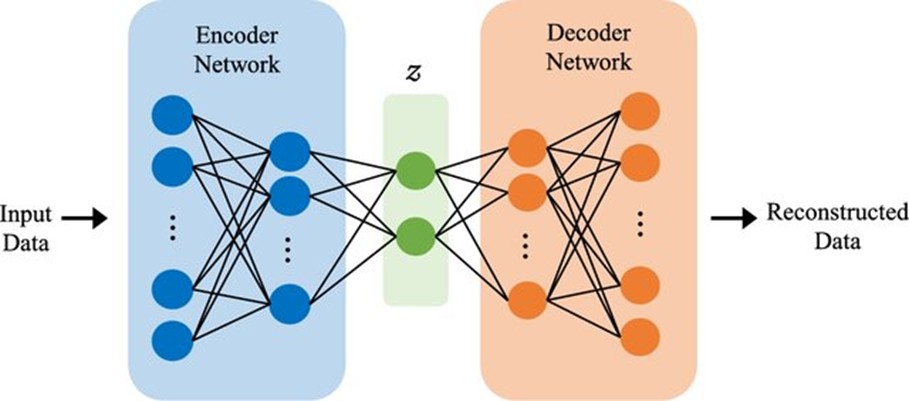
Credential compromise is one of the most widespread security threats, allowing adversaries to bypass traditional authentication measures and impersonate legitimate users. Traditional intrusion detection systems are often based on network-level or macro-behavioral indicators, which can be easily spoofed by an attacker, thus compromising the effectiveness of those mechanisms. This study presents an improved adaptive intrusion detection system to authenticate user behavior based on micro-digital behavioral profiling. It involves the use of timing of keystrokes, micro-mouse, navigation in the application, and interaction rhythm signatures. The proposed system uses a hybrid model consisting of Long Short-Term Memory (LSTM) sequence prediction and an Autoencoder reconstruction network to learn both structural and temporal variation of user behavior. Also, an adaptive learning module (implemented by a replay buffer and a drift-detection mechanism based on Kullback-Leibler divergence) to continually recalibrate the model when authentic user behavior varies. Experimental testing on a controlled set of 42 subjects in multiple sessions shows that the proposed model can achieve 94.8 0.91 F1-score and 0.05 false-positive rate, which outperforms the use of individual models; adaptive learning brings this number down by half in the case of drift. The comparison analysis proves the superiority of the proposed system in the areas of anomaly detection, stability, and real-time performance, which demonstrates the viability of micro-behavior analytics as a high-resolution security layer that can be used as a persistent authentication and identity-based threat detector.
Downloads
References
P. Garcia-Teodoro, J. Díaz-Verdejo, G. Maciá-Fernández, and E. Vázquez, “Anomaly-based network intrusion detection: Techniques, systems and challenges”, Computers & Security, vol. 28, no. 1–2, pp. 18–28, 2009.
H. J. Liao, C. H. R. Lin, Y. C. Lin, and K. Y. Tung, “Intrusion detection system: A comprehensive review,” J. Netw. Comput. Appl., vol. 36, no. 1, pp. 16–24, 2013.
A. L. Buczak and E. Guven, “A survey of data mining and machine learning methods for cybersecurity intrusion detection”, IEEE Commun. Surv. Tutor, vol. 18, no. 2, pp. 1153–1176, 2016.
R. Joyce and G. Gupta, “Identity authentication based on keystroke latencies”, Commun. ACM, vol. 33, no. 2, pp. 168–176, 1990.
K. S. Killourhy and R. A. Maxion, “Comparing anomaly-detection algorithms for keystroke dynamics,” in Proc. IEEE/IFIP Int. Conf. Dependable Systems & Networks, pp. 125–134, 2009.
J. Monaco, N. Bakelman, A. D. Kent, and C. C. Tappert, “Recent advances in keystroke biometrics”, in Proc. IEEE Int. Conf. Biometrics: Theory, Applications and Systems (BTAS), pp. 1–8, 2013.
A. A. E. Ahmed and I. Traore, “A new biometric technology based on mouse dynamics,” IEEE Trans. Depend Secure Comput., vol. 4, no. 3, pp. 165–179, 2007.
Alvaro Paricio-Garcia, Miguel A. Lopez-Carmona, Sergio Sierra-Arquero, “Analysis and evaluation of autoencoder-driven dimensionality reduction for face recognition pipelines”, Applied Soft Computing, vol. 172 (2025), pp: 112877, 2025.
Jiaqi Gao, Mingrui Fan, Yaru He, Daoqi Han, Yueming Lu, and Yaojun Qiao, “MACAE: memory module-assisted convolutional autoencoder for intrusion detection in IoT networks”, The Journal of Supercomputing, vol. 81, 2024.
Y. Zhang, H. Liu, and J. Wang, “Deep behavioral biometrics for continuous authentication: A survey,” IEEE Access, vol. 11, pp. 45231–45255, 2023.
S. Roy and D. Dasgupta, “Adaptive anomaly detection using hybrid deep learning models,” Computers & Security, vol. 134, 103302, 2024.
M. Alazab, S. Venkataraman, and R. Ranjan, “Behavioral-based intrusion detection using deep recurrent learning,” IEEE Transactions on Information Forensics and Security, vol. 19, pp. 1123–1137, 2024.
J. Kim and K. Park, “Continuous authentication using multimodal behavioral biometrics with LSTM–Autoencoder framework,” Expert Systems with Applications, vol. 235, 121246, 2025.
S. Hochreiter and J. Schmidhuber, “Long short-term memory,” Neural Comput., vol. 9, no. 8, pp. 1735–1780, 1997.
A. Sharma, P. Mishra, and K. Singh, “Real-time insider threat detection using behavioral sequence modeling,” Future Generation Computer Systems, vol. 154, pp. 98–110, 2025.
M. Wazid, A. K. Das, N. Kumar, and J. J. P. C. Rodrigues, “Multimodal behavioral biometrics-based continuous authentication for secure user access in cyber–physical systems,” Future Generation Computer Systems, vol. 156, pp. 233–245, 2025, doi: 10.1016/j.future.2024.02.019.
R. Alshowkan, K. Almarhabi, and S. Althunibat, “Continuous user authentication based on keystroke dynamics using machine learning techniques,” IEEE Access, vol 12, pp. 31245–31260, 2024, doi: 10.1109/ACCESS.2024.3367854.
Priya Bansal and Abdelkader Ouda, “ Continuous Authentication in the Digital Age: An Analysis of Reinforcement Learning and Behavioral Biometrics”, Computers, 13, 103, pp: 1-24, 2024.
S. Roy and D. Dasgupta, “Adaptive anomaly detection using hybrid deep learning models,” Computers & Security, vol. 134, Art. no. 103302, 2024, doi: 10.1016/j.cose.2023.103302.
M. Alazab, S. Venkataraman, and R. Ranjan, “Behavioral-based intrusion detection systems using deep learning,” IEEE Transactions on Information Forensics and Security, vol. 19, pp. 1123–1137, 2024, doi: 10.1109/TIFS.2023.3321562.
A. Sharma, P. Mishra, and K. Singh, “Real-time insider threat detection using behavioral sequence modeling,” Future Generation Computer Systems, vol. 154, pp. 98–110, 2025, doi: 10.1016/j.future.2024.01.015.
J. Kim and K. Park, “Continuous authentication using multimodal behavioral biometrics with LSTM–Autoencoder framework,” Expert Systems with Applications, vol. 235, Art. no. 121246, 2025, doi: 10.1016/j.eswa.2024.121246.
A. Alshamrani, S. Myneni, A. Chowdhary, and D. Huang, “A survey on advanced persistent threats: Techniques, solutions, challenges, and research opportunities,” IEEE Commun. Surv. Tutor., vol. 21, no. 2, pp. 1851–1877, 2019.
V. Chandola, A. Banerjee, and V. Kumar, “Anomaly detection: A survey,” ACM Comput. Surv., vol. 41, no. 3, pp. 1–58, 2009.
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Sura Abed Sarab Hussien, Mustafa S. Ibrahim Alsumaidaie, Nada Hussein M. Ali, Ayat Z. Al-Zouri

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.